This certificate is unique because it is installed on all of your Exchange servers. The subject for the certificate is "CN=Microsoft Exchange Server Auth Certificate" and does not contain any SAN names with references to specific servers.
It also has a 5-year lifetime. Which is just long enough for everyone to forget about it. I suspect that this certificate is due to expire in many organizations soon.
Today I got a call from an organization with the following symptoms:
- Outlook clients were slow to start
- Outlook clients were not displaying the user's calendar
- Outlook clients were not able to access Out-of-Office settings
- Everything was functioning fine the previous day
- No system changes had been made
- The organization is configured in hybrid mode with Exchange Online, but the issue was occurring for on-premises users
- Accessing through OWA was unaffected
The event information is:
Source: MSExchange Web Services Event ID: 24 The Exchange certificate [Subject] CN=Microsoft Exchange Server Auth Certificate [Issuer] CN=Microsoft Exchange Server Auth Certificate [Serial Number] 3329C02443B435A447B92E81EB177303 [Not Before] 2013-06-11 6:25:31 PM [Not After] 2018-05-16 6:25:31 PM [Thumbprint] DFC06BF3FC76974BCD1C050340998B65D5491007 expired on 2018-05-16 6:25:31 PM.
This certificate is not bound to IIS, so why is this expiration being noted by MSExchange Web Services?
The certificate used for authorization is set separately from IIS but is configurable. You can see the currently configured certificate by using Get-AuthConfig. The thumbprint for the certificate is listed in the CurrentCertificateThumbprint property.
If you've already been searching around related to this certificate, you've probably found some instructions on how to recreate it. However, if it is expired, you can just renew it instead by using the Exchange Admin Console. In servers > certificates, select Microsoft Exchange Server Auth Certificate and then click Renew in the details pane as shown below. The screen shot below is of a certificate that is not expired yet, it looks exactly the same other than the expiry date.
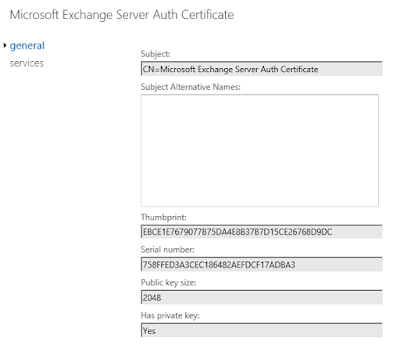
Renewing creates a second certificate named Microsoft Exchange Server Auth Certificate that is valid for another 5 years. This certificate has a new thumbprint and exists only on the server you've renewed it on. You need to identify the thumbprint for the new certificate. If you edit the certificate, in Exchange Admin Center, the thumbprint is on the general tab as shown below. You can type this in, but you're probably better of to cut and paste it into the later commands.
My preference is to put the required information for the next command into variable. We need the thumbprint of the new certificate and the current date.
$thumb = "NewCertificateThumbprint" $date = get-date
Then run the following command to add the new certificate:
Set-AuthConfig -NewCertificateThumbprint $thumb -NewCertificateEffectiveDate $date
You will get a warning that the new effective date is not 48 hours in the future. However, if we're recovering from an expired certificate, we're OK with that.
Now you need to publish the certificate to all servers:
Set-AuthConfig -PublishCertificate
And finally, remove the old expired certificate from the configuration:
Set-AuthConfig -ClearPreviousCertificate
Finally, since we've removed all references to the expired certificate you can delete it from all Exchange servers.
You may find that you need to do an iisreset after all of the AuthConfig changes were done. I found some examples where they ran iisreset.exe and didn't take the time to experiment. It's possible that it will pickup without a restart but just take longer.
I've added another post related to the Auth certificate and hybrid deployments here:




nice post
ReplyDeletewhen renewing the OAuth cert, does this need to be uploaded to Office 365? This occurred in our environment and now the migration endpoint admin account won't authenticate to perform any email migrations from on prem to o365
Thanks for the steps!, Q1, in env that have hybrid with exchange 365 - ware they any steps that need to be taken after renew OAuth on premises?
ReplyDeleteQ2 on-premises Skype 2015, what are the additional steps for OWA integration with Skype so users will still be able to "Online Meeting"
Thanks, I see that after renew the oauth on ex the eDiscovery is failing for user that have on prem mailbox with online archive, so we will probably have to re-run the export/import for 365 https://docs.microsoft.com/en-us/exchange/configure-oauth-authentication-between-exchange-and-exchange-online-organizations-exchange-2013-help#step-3-export-the-on-premises-authorization-certificate
ReplyDeleteRerunning the hybrid wizard might fix it up also.
ReplyDeleteThank you. Need to renew my certificate this weekend and this blog has been very helpful.
ReplyDeleteI'm still unsure if this will have any impact on my hybrid so I am expecting to have to run the hybrid wizard again.
@ Rika, if possible, can you let me know if running the wizard again did fix your issue?
Thanks.
in my env I had to run step 3 & 4 to export and upload the new auth cert from on-premises to 365 https://docs.microsoft.com/en-us/exchange/configure-oauth-authentication-between-exchange-and-exchange-online-organizations-exchange-2013-help
ReplyDeleteand tested successfully Test-OAuthConnectivity -Service AutoD -TargetUri https://autodiscover-s.outlook.com/autodiscover/autodiscover.svc -mailbox -verbose |fl
I renewed my auth cert yesterday, tried to export and import the cert as step 3 and 4 above but this didn't work. Test-OAuthConnectivity showing errors and free/busy info not showing when on-prem user looked at an online user. Re-ran hybrid wizard which resolved the issue immediately.
ReplyDeleteOnce again, thanks for the blog and replies from Rika.
Thanks for taking the time to post this article. Our Auth Certificate expires in December so I went into ECP and hit the renew link to knock this out before I forget about it. Contrary to what you posted above it did create a new certificate. Now I am assuming that I will need to follow the above steps as if it had expired?
ReplyDeleteRunning steps 3 & 4 from the doc also worked for us after renewing the cert.
ReplyDeletehttps://docs.microsoft.com/en-us/exchange/configure-oauth-authentication-between-exchange-and-exchange-online-organizations-exchange-2013-help
Is it type "Set-AuthConfig -PublishCertificate" in the command prompt for publish the certificate?
ReplyDeleteYou run that command in the Exchange Management Shell (EMS). That is Windows PowerShell with the Exchange specific management cmdlets.
Deleteany additional steps needed if also running Sharepoint and Skype for Business?
ReplyDeleteIf I had renew the auth cert from EAC, do I need to publish it?
ReplyDeleteHow to publish? By cmd (exchange pwrsheel?
If i renew it from console before expiry. I just need to do below
ReplyDelete1. Renew from exchange console
2. run command "Set-AuthConfig -PublishCertificate"
Please confirm
Ideally you have to create new certificate anyways as the original certificate is only SHA1 type and we need to be on SHA2, not sure how Microsoft missed that
ReplyDeleteforgot to add how to view certificates for SHA1 or SHA2 types
ReplyDeleteOpen Exchange powershell console as admin and type
Get-ExchangeCertificate | Select Subject, thumbprint, services -ExpandProperty SignatureAlgorithm
If FriendlyName is sha256RSA or similar you have SHA2 type certificate
If FriendlyName is sha1RSA you have old bad SHA1 type certificate
Hi, I renew certificate then issue command Set-AuthConfig –PublishCertificate but I got error message 'the certificate that can be used next must be established before it can be published.' Any suggestion why this error come up? Perhaps the certificate doesn't need to be published? Thanks for your advice.
ReplyDeleteHi, I have the same. Do you have a sollution?
DeleteIn our 2013 hybrid environment, even though i renewed the certificate from ECP 1 week before expiry, a new certificate with different thumbprint was created. I had to follow all the steps mentioned in this article and also configure Oauth in Azure using steps 3 and 4 in MS article. Hope this helps someone.
ReplyDeleteIf the certificate is about to expire in 2 weeks, and we have 16 servers, do I need to renew it on each on or will it just apply to all when I do the renew? (2016 exchange)
ReplyDeleteYou renew only on one server. Then you publish to all servers with: Set-AuthConfig -PublishCertificate
DeleteI normally don't post "thank you" comments but I will now: thank you
ReplyDeleteIs it also possible, to create an Certificate from a Root CA (ex GoDaddy) and set it as the Auth Certificate? Reason: Skype and Azure Voice Mail does not know the Exchange internal Certificate.
ReplyDeleteI'm not familiar with the details of Skype and Azure Voice Mail, for the Auth certificate, but are you sure a cert from a public CA is required for authentication? Exchange 2019 creates a self-signed auth certificate that's use for hybrid authentication. That leads me to believe it's sufficient for O365 servers. You will definitely need a cert from a public CA for IIS services.
DeleteTo answer the question, I haven't tried with a cert from the public CA, but I think it would probably work. However, the lifetime on a cert from a public CA is a maximum of 2 years which means it will expire faster than using the self signed cert.
DeleteRenew certificate using ECP but failed at step Set-AuthConfig -NewCertificateThumbprint with error "Couldn't find the certificate with the specified thumbprint". Is that due to sha1RSA type?
ReplyDeleteThe most likely issue is incorrectly copying the thumbprint. Double-check the properties of the renewed cert to make sure you copied the thumbprint correctly.
Deletethank you for your posts. it keeps me frustrated since the old expired certificates keep coming back. I used ECP to renew it, it works greatly for me.
ReplyDelete