When you install your first Exchange Server 2013 or Exchange Server 2016 server, a certificate with the friendly name Microsoft Exchange Server Auth Certificate is created. This certificate is self-signed and used for OAuth authentication between applications such as Exchange Server and SharePoint. However, it is also used for hybrid deployments between on-premises Exchange Server and Exchange Online.
This certificate is unique because it is installed on all of your Exchange servers. The subject for the certificate is "CN=Microsoft Exchange Server Auth Certificate" and does not contain any SAN names with references to specific servers.
It also has a 5-year lifetime. Which is just long enough for everyone to forget about it. I suspect that this certificate is due to expire in many organizations soon.
Today I got a call from an organization with the following symptoms:
- Outlook clients were slow to start
- Outlook clients were not displaying the user's calendar
- Outlook clients were not able to access Out-of-Office settings
- Everything was functioning fine the previous day
- No system changes had been made
- The organization is configured in hybrid mode with Exchange Online, but the issue was occurring for on-premises users
- Accessing through OWA was unaffected
An initial review of the configuration didn't identify anything out of the ordinary except that the Microsoft Exchange Server Auth Certificate had expired about two weeks ago. There was also this related event in the Application log:
The event information is:
Source: MSExchange Web Services
Event ID: 24
The Exchange certificate [Subject]
CN=Microsoft Exchange Server Auth Certificate
[Issuer]
CN=Microsoft Exchange Server Auth Certificate
[Serial Number]
3329C02443B435A447B92E81EB177303
[Not Before]
2013-06-11 6:25:31 PM
[Not After]
2018-05-16 6:25:31 PM
[Thumbprint]
DFC06BF3FC76974BCD1C050340998B65D5491007
expired on 2018-05-16 6:25:31 PM.
This certificate is not bound to IIS, so why is this expiration being noted by MSExchange Web Services?
The certificate used for authorization is set separately from IIS but is configurable. You can see the currently configured certificate by using Get-AuthConfig. The thumbprint for the certificate is listed in the CurrentCertificateThumbprint property.
If you've already been searching around related to this certificate, you've probably found some instructions on how to recreate it. However, if it is expired, you can just renew it instead by using the Exchange Admin Console. In servers > certificates, select Microsoft Exchange Server Auth Certificate and then click Renew in the details pane as shown below. The screen shot below is of a certificate that is not expired yet, it looks exactly the same other than the expiry date.
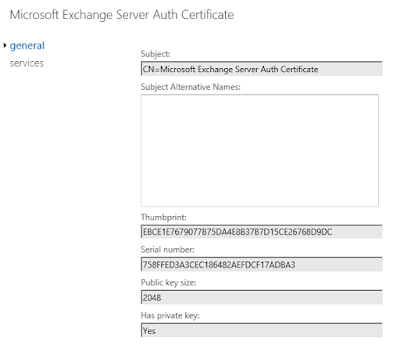
Renewing creates a second certificate named Microsoft Exchange Server Auth Certificate that is valid for another 5 years. This certificate has a new thumbprint and exists only on the server you've renewed it on. You need to identify the thumbprint for the new certificate. If you edit the certificate, in Exchange Admin Center, the thumbprint is on the general tab as shown below. You can type this in, but you're probably better of to cut and paste it into the later commands.
My preference is to put the required information for the next command into variable. We need the thumbprint of the new certificate and the current date.
$thumb = "NewCertificateThumbprint"
$date = get-date
Then run the following command to add the new certificate:
Set-AuthConfig -NewCertificateThumbprint $thumb -NewCertificateEffectiveDate $date
You will get a warning that the new effective date is not 48 hours in the future. However, if we're recovering from an expired certificate, we're OK with that.
Now you need to publish the certificate to all servers:
Set-AuthConfig -PublishCertificate
And finally, remove the old expired certificate from the configuration:
Set-AuthConfig -ClearPreviousCertificate
Finally, since we've removed all references to the expired certificate you can delete it from all Exchange servers.
You may find that you need to do an iisreset after all of the AuthConfig changes were done. I found some examples where they ran iisreset.exe and didn't take the time to experiment. It's possible that it will pickup without a restart but just take longer.
I've added another post related to the Auth certificate and hybrid deployments here: